Are request headers secure
The headers are entirely encrypted. The only information going over the network ‘in the clear’ is related to the SSL setup and D/H key exchange. This exchange is carefully designed not to yield any useful information to eavesdroppers, and once it has taken place, all data is encrypted.
Can HTTP headers be hacked?
It could even happen if your site displays the ‘s’ as in HTTPS… Some people will, and some won’t, yet many people don’t realise the issues that this can cause if your headers are hacked. The worrying thing is, that it can happen to anyone even if you are a person who works within or even owns a technology business.
Are HTTP headers protected by SSL?
Strictly speaking, HTTPS is not a separate protocol, but refers to the use of ordinary HTTP over an encrypted SSL/TLS connection. HTTPS encrypts all message contents, including the HTTP headers and the request/response data.
What are secure headers?
Security headers are directives used by web applications to configure security defenses in web browsers. Based on these directives, browsers can make it harder to exploit client-side vulnerabilities such as Cross-Site Scripting or Clickjacking.Are headers more secure than parameters?
From the security point of view, there’s no difference on using HTTP Header vs Query Param since both are encrypted when using TLS/SSL. But query params can be more fragile since it can be easily visible in browsers, are logged across the board by default (browser history, web servers access logs and etc).
Is Host header mandatory?
If your question is “why specify the host in a Host header as opposed to on the Request-Line”, the answer is the need for interopability between HTTP/1.0 and 1.1. If the question is “why is the Host header mandatory”, this has to do with the desire to speed up the transition away from assigned IP addresses.
Can Host Header be spoofed?
It allows for domain-based virtual hosting, where websites on multiple domains are hosted on a single web server. It is trivial to spoof HTTP requests and the Host header is no exception. … In some cases, using a spoofed Host header can be used to bypass filters that block traffic based on the content of this header.
Are security headers important?
Why HTTP Security Headers are necessary ? As you know, nowadays too many data breaches are happening, many websites are hacked due to misconfiguration or lack of protection. These security headers will protect your website from some common attacks like XSS, code injection, clickjacking, etc.What security request headers have been included?
- HTTP Strict Transport Security (HSTS) …
- Content Security Policy (CSP) …
- Cross Site Scripting Protection (X-XSS) …
- X-Frame-Options. …
- X-Content-Type-Options.
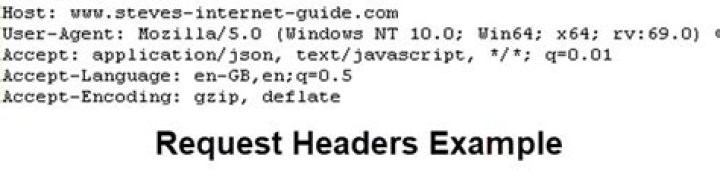
An HTTP header consists of its case-insensitive name followed by a colon ( : ), then by its value. Whitespace before the value is ignored.
Article first time published onAre HTTP requests encrypted?
All HTTP requests and responses are then encrypted with these session keys, so that anyone who intercepts communications can only see a random string of characters, not the plaintext. In addition to encrypting communication, HTTPS is used for authenticating the two communicating parties.
Are GET requests encrypted?
11 Answers. The entire request is encrypted, including the URL, and even the command ( GET ). The only thing an intervening party such as a proxy server can glean is the destination address and port.
Are post requests encrypted?
HTTP POST is not encrypted, it can be intercepted by a network sniffer, by a proxy or leaked in the logs of the server with a customised logging level. Yes, POST is better than GET because POST data is not usualy logged by a proxy or server, but it is not secure.
What is the difference between request header and body?
The start-line and HTTP headers of the HTTP message are collectively known as the head of the requests, whereas its payload is known as the body.
Are cookies just headers?
A cookie is an HTTP request header i.e. used in the requests sent by the user to the server. … It is an optional header.
Is header more secure than body?
2 Answers. Header is more convenient for the server. Imagine an API where you upload a file as a body for PUT – if token was also in body, you’d have to deal with encoding the body some way to make it clear what is the token and what is the uploaded file.
What is host header poisoning?
Host header attacks may be used for web cache poisoning and attacks such as password reset poisoning. Web cache poisoning lets an attacker serve poisoned content to anyone who requests pages. Using password reset poisoning, the attacker can obtain a password reset token and reset another user’s password.
How does HTTP header injection happen?
Description: HTTP response header injection If an attacker can inject newline characters into the header, then they can inject new HTTP headers and also, by injecting an empty line, break out of the headers into the message body and write arbitrary content into the application’s response.
What is impact of host header injection?
Impact: Tampering of Host header can lead to the following attacks: 1) Web Cache Poisoning-Manipulating caching systems into storing a page generated with a malicious Host and serving it to others.
What HTTP headers are mandatory?
Common Response Headers The first line of the response is mandatory and consists of the protocol ( HTTP/1.1),response code (200)and description (OK). The headers shown are: CONTENT-Type -This is Text/html which is a web page. It also includes the character set which is UTF-8.
How do I remove the header from Host?
By removing the Host header, you’re essentially downgrading your request to HTTP/1.0. You can set the HTTP version in the HttpRequestMessage as explained in Set HTTP protocol version in HttpClient: msg. Version = HttpVersion.
What headers are required for post request?
- Standard headers. A-IM. Accept. Accept-Charset. Accept-Encoding. Accept-Language. Accept-Datetime. Access-Control-Request-Method. …
- Non-standard headers. Dnt. X-Requested-With. X-CSRF-Token.
Is HTTP 1.1 secure?
Authentication Credentials Existing HTTP clients and user agents typically retain authentication information indefinitely. HTTP/1.1 does not provide a method for a server to direct clients to discard these cached credentials which is a big security risk.
Are response headers secure?
HTTP Response Headers allow server to pass additional information with the response, which instruct the browser how to behave when handling sensitive contents and data’s of the application. Http response security headers provide an extra protection layer which help to mitigate vulnerabilities and attacks.
What expect-CT header?
The Expect-CT header lets sites opt in to reporting and/or enforcement of Certificate Transparency requirements, to prevent the use of misissued certificates for that site from going unnoticed.
How do I add permission policy to header?
You can find the Permissions Header policy settings in the Premium tab from your Really Simple SSL Dashboard (Settings -> SSL -> Premium). To enable the Permission Policy header, enable the ‘Permissions Policy’ option. Once enabled, a new block containing a list of directives and their values will appear.
How do I hide the header request in browser?
1 Answer. It is not possible to hide this token. However if you use HTTPS, the connection to your website is secure and no one in the middle can see it. The token is only visible to the user that it belongs to, so it poses no security risk as the user should have access to it.
How can HTTP Security headers improve web application security?
HTTP security headers provide an extra layer of security by restricting behaviors that the browser and server allow once the web application is running.
Are request headers case insensitive?
Header names are not case sensitive. From RFC 2616 – “Hypertext Transfer Protocol — HTTP/1.1”, Section 4.2, “Message Headers”: Each header field consists of a name followed by a colon (“:”) and the field value.
Should authorization header be capitalized?
On the other hand, RFC 6750 section 2.1 states that the Authorization header scheme for bearer tokens must be capitalized: Clients should make authenticated requests with a bearer token using the “Authorization” request header field with the “Bearer” HTTP authorization scheme.
Do headers need to be capitalized?
Just follow these simple rules. Capitalize the first word of the title or heading. … All other words are capitalized unless they are conjunctions (and, or, but, nor, yet, so, for), articles (a, an, the), or prepositions (in, to, of, at, by, up, for, off, on).



