What does data access mean
Data access is the on-demand, authorized ability to retrieve, modify, copy, or move data from IT systems. … Data access is the means by which users can get to this data and its location, in an authenticated manner approved by the organization in possession of the data.
What is meant by user access level?
User access levels define what information the different users on your account can access and edit. They are particularly important for when you want to keep your employees’ hourly rates confidential.
Why is access level important?
Access levels are permission sets that allow members to perform different tasks within an organization. By assigning organization members to access levels, you determine the information they can see and actions they are allowed to perform.
What is access in data processing?
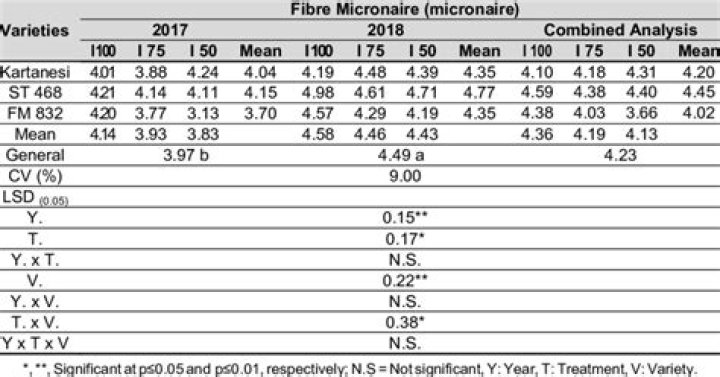
Data access crucially involves authorization to access different data repositories. Data access can help distinguish the abilities of administrators and users. … Some of these standards enable translation of data from unstructured (such as HTML or free-text files) to structured (such as XML or SQL).What are the access data types?
Data TypeUsageSizeNumberNumeric data.1, 2, 4, 8, or 16 and times.8 bytes.CurrencyMonetary data, stored with 4 decimal places of precision.8 bytes.AutoNumberUnique value generated by Access for each new record.4 bytes (16 bytes for ReplicationID).
How does setting levels help protect data?
If anyone can edit the database, data could easily become corrupted . It is better to have different levels of access for the database to maintain the integrity of the database. For example, with personalised websites that require a login, you will only see data that is relevant to you.
What is the use of Access?
Microsoft Access is an information management tool, or relational database, that helps you store information for reference, reporting and analysis. Access can also overcome the limitations found when trying to manage large amounts of information in Excel or other spreadsheet applications.
What is access right in database?
A data access right (DAR) is a permission that has been granted that allows a person or computer program to locate and read digital information at rest. Digital access rights play and important role in information security and compliance.Why might two users in the same network have different access levels?
Access levels The more people have access to sensitive parts of the network, the more likely it is that a hacker or a virus might be able to cause damage. You can set user access levels on your home computer.
What is data access and management?Data Access Management is a set of processes and technologies used to control access to application or data. It involves creation of groups or roles with defined access privileges and then controlling access by defining group memberships. … Applications.
Article first time published onWhy is the level of access important to be applied in every organization?
Access controls limit access to information and information processing systems. When implemented effectively, they mitigate the risk of information being accessed without the appropriate authorisation, unlawfully and the risk of a data breach.
What is access level in Java?
Java access level contains two parts: 1) access level for classes and 2) access level for members. … Access level determines the accessibility of fields and methods. It has 4 levels: public, protected, package-private (no explicit modifier), or private.
What is the connection between user access level and security in computer systems?
User access security refers to the collective procedures by which authorized users access a computer system and unauthorized users are kept from doing so.
What are the 5 types of data?
- Integer.
- Floating-point number.
- Character.
- String.
- Boolean.
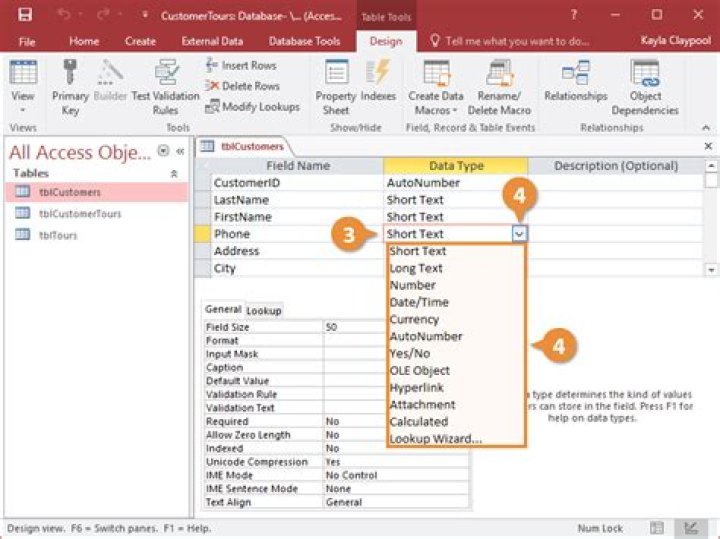
What are the 4 objects in Access?
Within Access there are four major objects: Tables, Queries, Forms and Reports.
What are the types of data in database?
Some common data types are as follows: integers, characters, strings, floating point numbers and arrays. More specific data types are as follows: varchar (variable character) formats, Boolean values, dates and timestamps.
Is Access the same as SQL?
Microsoft Access and Microsoft SQL Server are both database applications. The major difference between the two is in how the software is used. Microsoft Access is used in home or small business applications. … Microsoft SQL Server is for medium to large businesses that need a solution for better data processing.
What is difference between Excel and Access?
The main difference between Excel and Access is that Excel is a spreadsheet to perform calculations and to represent data visually while Access is a Database Management System that is used to store and manage data easily. … Overall, Excel is a spreadsheet, whereas Access is a DBMS.
Can I use SQL in Access?
Relational database programs, such as Microsoft Office Access, use SQL to work with data. Unlike many computer languages, SQL is not difficult to read and understand, even for a novice. … Note: SQL is not only used for manipulating data, but also for creating and altering the design of database objects, such as tables.
Why is it important to control access to data in a database?
The ultimate aim of access control is to provide a level of security that minimises risk to a business or organisation by helping to keep buildings, data and people secure. This is why access control goes hand in hand with I.T security and should be a key consideration for every business owner.
What are the 3 types of access control?
Three main types of access control systems are: Discretionary Access Control (DAC), Role Based Access Control (RBAC), and Mandatory Access Control (MAC).
What are the benefits of access control?
- Increase Ease of Access for Employees. …
- Get Rid of Traditional Keys. …
- Save Money and Energy. …
- Keep Track of Who Comes and Goes. …
- Protect Against Unwanted Visitors. …
- Give Employees the Freedom to Work When They Need To. …
- Prevent Against Data Breaches.
What are the two types of access permission?
Access permissions include read, write, and none.
How do I manage users in Windows Server?
- Open the Windows Server Essentials Dashboard.
- On the navigation bar, click Users.
- In the list view, select the user account that you want to activate.
- In the <User Account> Tasks pane, click Activate the user account.
- In the confirmation window, click Yes to confirm your action.
Why are permissions important to sharing in Windows?
Through the use of permissions, Windows defines which user accounts and user groups can access which files and folders, and what they can do with them. To put it simply, permissions are the operating system’s way of telling you what you can or cannot do with a file or folder.
What is an access defined and applied to?
Microsoft Access, often abbreviated “MS Access,” is a popular database application for Windows. Access allows users to create custom databases that store information in an organized structure. … This allows data to be sent to and from other database programs, such as MS SQL, FoxPro, Filemaker Pro, and Oracle databases.
How do I secure my computer network?
- Install and monitor firewall performance.
- Update passwords at least every quarter.
- Lean on Advanced Endpoint Detection.
- Create a virtual private network (VPN)
- Train your employee.
- Filter and delete spam emails.
- Shut down computers when not in use.
- Encrypt your files.
How can network data be made more secure?
- making regular backups of files (backup copies should be stored in fireproof safes or in another building)
- protecting yourself against viruses by running anti-virus software.
- using a system of passwords so that access to data is restricted.
How do you access data?
There are two ways to access stored data: random access and sequential access. The sequential method requires information to be moved within the disk using a seek operation until the data is located. Each segment of data has to be read one after another until the requested data is found.
How is access to data controlled?
Access control is a fundamental component of data security that dictates who’s allowed to access and use company information and resources. Through authentication and authorization, access control policies make sure users are who they say they are and that they have appropriate access to company data.
What is and access right?
Access Rights are the permissions an individual user or a computer application holds to read, write, modify, delete or otherwise access a computer file; change configurations or settings, or add or remove applications.