What is a security diagram
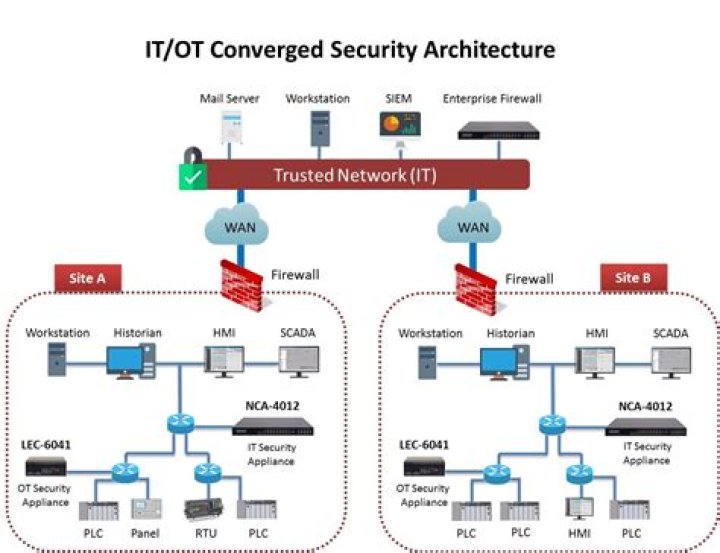
The purpose of the data security diagram is to depict which actor (person, organization, or system) can access which enterprise data. This relationship can be shown in matrix form between two objects or can be shown as a mapping.
What is a network diagram in IT security?
A network diagram is a visual representation of a computer or telecommunications network. It shows the components that make up a network and how they interact, including routers, devices, hubs, firewalls, etc.
What is a network diagram called?
There are two main types of network diagrams in project management: the arrow diagramming method (ADM), also known as “activity network diagram” or “activity on arrow”; and the precedence diagramming method (PDM), also known as “node network” or “activity on node.”
What is the role of the network diagram?
Network Diagrams are a graphical portrayal of the activities and events of a project. They show how each activity relates to others in the project, the sequence of activities, and the need to perform some tasks before others.What is security architecture and design?
Security architecture and design looks at how information security controls and safeguards are implemented in IT systems in order to protect the confidentiality, integrity, and availability of the data that are used, processed, and stored in those systems.
What is network security in simple words?
Network security is any activity designed to protect the usability and integrity of your network and data. It includes both hardware and software technologies. It targets a variety of threats. It stops them from entering or spreading on your network. Effective network security manages access to the network.
What is data Dissemination diagram?
The purpose of the data dissemination diagram is to show the relationship between data entities, business services, and application components. The diagram shows how the logical entities are to be physically realized by application components.
What is the use of network security?
Network Security protects your network and data from breaches, intrusions and other threats. This is a vast and overarching term that describes hardware and software solutions as well as processes or rules and configurations relating to network use, accessibility, and overall threat protection.What is network security with example?
Network security is protection of the access to files and directories in a computer network against hacking, misuse and unauthorized changes to the system. An example of network security is an anti virus system. noun. (1) The authorization of access to data in a network, which is controlled by the network administrator …
What are the benefits of network diagram?- Network diagrams show interdependencies of activities. …
- Network Diagrams show workflow of the project activities. …
- Network diagrams identify opportunities to compress the schedule. …
- Network diagrams show project progress.
What is network diagram and critical path?
The critical path is the longest path of the network diagram. The activities in the critical path have an effect on the deadline of the project. If an activity of this path is delayed, the project will be delayed.
How do you create a network diagram?
- Select a network diagram template. …
- Name the network diagram. …
- Remove existing elements that you don’t need on your diagram. …
- Add network components to the diagram. …
- Name the items in your network diagram. …
- Draw connections between components. …
- Add a title and share your network diagram.
What is a layer 3 network diagram?
Diagrams are intended to convey information to the reader, so it is fundamental to decide what is to be conveyed. … Layer 3 refers to the thrid layer of the OSI model – the network layer.
What is a current network diagram?
2: Current network diagram that identifies all connections between the cardholder data environment and other networks, including any wireless networks Network diagrams describe how networks are configured, and identify the location of all network devices.
What are the 7 layers of security?
The OSI model’s seven layers are the: Human Layer, Perimeter Layer, Network Layer, Endpoint Layer, Application Layer, Data Layer, and Mission Critical Layer.
What is CIA triad in cyber security?
These three letters stand for confidentiality, integrity, and availability, otherwise known as the CIA triad. Together, these three principles form the cornerstone of any organization’s security infrastructure; in fact, they (should) function as goals and objectives for every security program.
What are the three elements of security?
The CIA triad refers to an information security model made up of the three main components: confidentiality, integrity and availability.
What is viewpoint in Togaf?
Viewpoints uniquely identify each set of stakeholder & their unique set of concerns. With this viewpoint in mind, the architect creates views that capture the current state architecture and the future state architecture with new capabilities while shedding light on the concerns of the stakeholder.
What is data architecture Togaf?
Data architecture describes the structure of an organization’s logical and physical data assets and data management resources, according to The Open Group Architecture Framework (TOGAF). … An organization’s data architecture is the purview of data architects.
What is a solution concept diagram?
A solution concept diagram provides a high-level orientation of the solution that is envisaged in order to meet the objectives of the architecture engagement.
What are the components of network security?
Firewalls, IPS, network access control (NAC), and security information and event management (SIEM) are the four most essential components of network security. Others include data loss prevention (DLP); antivirus and anti-malware software; application, web and email security; and more.
What are the 5 types of security?
- Critical Infrastructure Cybersecurity. The critical infrastructure cybersecurity technique is deployed to secure the systems that have the critical infrastructure. …
- Network Security. …
- Cloud Security. …
- Internet of Things Security. …
- Application Security.
What is the best network security?
- Bitdefender — Best network security software for most.
- Avast CloudCare — Best for MSPs managing multiple networks.
- Firemon — Best for automated network security.
- Watchguard — Best for real-time network visibility.
- Qualys — Best for network vulnerability management.
What is network security tools?
Network Security Tools. Network security tools can be either software- or hardware-based and help security teams protect their organization’s networks, critical infrastructure, and sensitive data from attacks. … These include tools such as firewalls, intrusion detection systems and network-based antivirus programs.
What are the disadvantages of network diagrams?
Disadvantages of applying project network diagrams Project network diagrams are not exclusion. Creating such a diagram takes time and costs money to produce it. Sometimes network diagrams can be too complex and difficult to discern visually. There can also be errors when making it or other factors that can influence.
What are the rules for drawing network diagram?
f) The flow of the diagram should be from left to right. g) Two events are numbered in such a way that the event of higher number can happen only after the event of lower number is completed. h) Arrows should be kept straight and not curved. Avoid arrow which cross each other.
How do you create a network diagram in project management?
- Begin your project with a single milestone and label it Start.
- Find all activities in the table that have no immediate predecessors — they can all start as soon as you begin your project. …
- Begin your diagram by drawing the relationship between the Start of your project and the beginning of Activity 5.
What is critical path diagram?
The critical path method (CPM), also known as critical path analysis (CPA), is a scheduling procedure that uses a network diagram to depict a project and the sequences of tasks required to complete it, which are known as paths.
How do I create a network diagram online?
- Step 1 – Open Edraw Max Online.
- Step 2 – Open Information Technique.
- Step 3 – Create a Network Diagram.
- Step 4 – Customize your Network Diagram.
- Step 5 – Save you File.
What is a Layer 1 network diagram?
Drawing Layer 1 diagrams Layer 1 diagrams should show port numbers and indicate cable types. In a network that includes many different types of cables, such as fiber optic cables, Category 5/6/7 copper cabling, and so forth, it’s useful to give each cable type a different color.
What is difference between l2 and l3 switch?
A Layer 2 switch only works with MAC addresses and doesn’t interact with any higher layer addresses, such as an IP. A Layer 3 switch, on the other hand, can also do static routing and dynamic routing, which includes IP and virtual local area network (VLAN) communications.