What is OAuth 2.0 used for
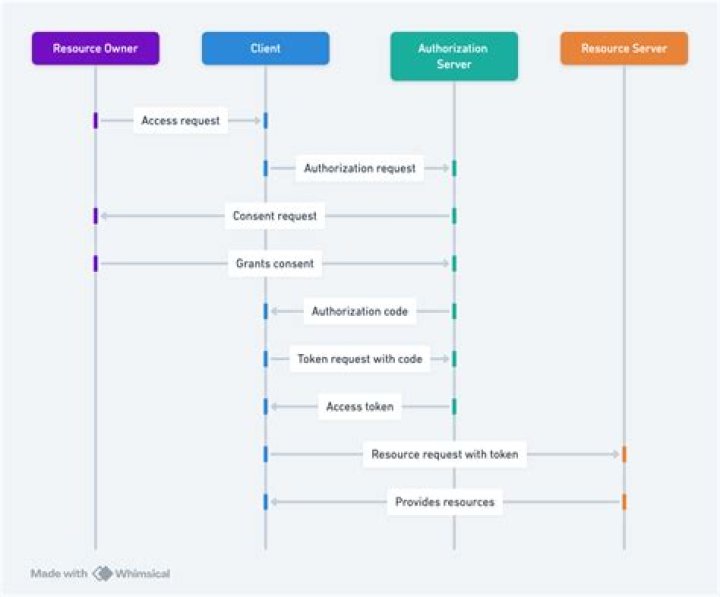
OAuth 2.0 is an authorization framework for delegated access to APIs. It involves clients that request scopes that Resource Owners authorize/give consent to. Authorization grants are exchanged for access tokens and refresh tokens (depending on flow).
What does O in OAuth mean?
The more you give away your passwords, the more likely it is that your passwords will get compromised. That’s where OAuth comes in. OAuth, which stands for “Open Authorization,” allows third-party services to exchange your information without you having to give away your password.
Why OAuth 2.0 is bad?
Bad OAuth 2.0 implementation is a mobile app security risk In addition, any data residing within the victim app is also available to the attacker. And any of these scenarios are possible without access to a user’s device or having to know the user’s password. An attacker only needs to know (or guess) a user’s ID.
What is OAuth 2.0 and how it works?
The OAuth 2.0 authorization framework is a protocol that allows a user to grant a third-party web site or application access to the user’s protected resources, without necessarily revealing their long-term credentials or even their identity.What is difference between OAuth 1.0 and OAuth 2 O?
OAuth 2.0 signatures are not required for the actual API calls once the token has been generated. It has only one security token. OAuth 1.0 requires client to send two security tokens for each API call, and use both to generate the signature.
What is OAuth 2.0 in spring boot?
OAuth2 is an authorization framework that enables the application Web Security to access the resources from the client. To build an OAuth2 application, we need to focus on the Grant Type (Authorization code), Client ID and Client secret.
What is Auth0 vs OAuth?
OAuth 2.0 is a protocol that allows a user to grant limited access to their resources on one site, to another site, without having to expose their credentials. Auth0 is an organisation, who manages Universal Identity Platform for web, mobile and IoT can handle any of them — B2C, B2B, B2E, or a combination.
What is state in OAuth2?
The state parameter is a string so you can encode any other information in it. You send a random value when starting an authentication request and validate the received value when processing the response.What is OAuth 2.0 in C#?
OAuth is a token based authorization mechanism for REST Web API. You develop the authorization with the API only once up until the expiration time of the token. The generated token is then used each time the REST Web API is called, saving an authorization step every time the REST Web API is called.
What is oauth2 proxy?oauth2-proxy is a reverse proxy and static file server that provides authentication using Providers (Google, GitHub, and others) to validate accounts by email, domain or group.
Article first time published onWhat is callback URL in oauth2?
Callback URL. A callback URL is the URL that is invoked after OAuth authorization for the consumer (connected app). In some contexts, the URL must be a real URL that the client’s web browser is redirected to.
How do I add OAuth to my API?
- In a command window, change to the project folder that you created in the tutorial Tutorial: Creating an invoke REST API definition.
- In the API Designer, click the APIs tab.
- Click Add > OAuth 2.0 Provider API.
- Complete the fields according to the following table: …
- Click Create API.
Why is OAuth2 more secure?
OAuth 2.0 is a more straightforward protocol passing the client secret with every authentication request. Therefore, this protocol is not backward compatible with OAuth 1.0. Moreover, it is deemed less secure because it relies solely on the SSL/TLS layer.
Can OAuth be hacked?
An attacker can exploit this by registering an account with the OAuth provider using the same details as a target user, such as a known email address. Client applications may then allow the attacker to sign in as the victim via this fraudulent account with the OAuth provider.
Should I use OAuth?
When to Use OAuth You should only use OAuth if you actually need it. If you are building a service where you need to use a user’s private data that is stored on another system — use OAuth. If not — you might want to rethink your approach!
What is oauth2 vs OAuth?
OAuth 2.0 is a complete rewrite of OAuth 1.0 from the ground up, sharing only overall goals and general user experience. OAuth 2.0 is not backwards compatible with OAuth 1.0 or 1.1, and should be thought of as a completely new protocol.
Is OAuth 1 obsolete?
Important: OAuth 1.0 has been officially deprecated as of April 20, 2012. It will continue to work as per our deprecation policy, but we encourage you to migrate to OAuth 2.0 as soon as possible.
What is the difference between OAuth and bearer token?
The Bearer Token is created for you by the Authentication server. When a user authenticates your application (client) the authentication server then goes and generates for you a Token. Bearer Tokens are the predominant type of access token used with OAuth 2.0. … You use the bearer token to get a new Access token.
How is SAML different from OAuth?
Security Assertion Markup Language (SAML) and Open Authorization (OAuth) have emerged as the go-to technologies for federated authentication. While SAML is an Extensible Markup Language (XML)-based standard, OAuth is based on JavaScript Object Notation (JSON), binary, or even SAML formats.
Is OAuth2 authentication or authorization?
OAuth 2.0 is an authorization protocol and NOT an authentication protocol. As such, it is designed primarily as a means of granting access to a set of resources, for example, remote APIs or user’s data.
Is OAuth a SSO?
OAuth is one of the most common methods used to pass authorization from a single sign-on (SSO) service to another cloud application, but it can be used between any two applications.
How OAuth2 works in Spring Security?
A Resource Server serves resources that are protected by the OAuth2 token. Spring OAuth2 provides an authentication filter that handles protection. The @EnableResourceServer annotation enables a Spring Security filter that authenticates requests via an incoming OAuth2 token.
What is Grant type in OAuth2?
In OAuth 2.0, the term “grant type” refers to the way an application gets an access token. … Each grant type is optimized for a particular use case, whether that’s a web app, a native app, a device without the ability to launch a web browser, or server-to-server applications.
What is OAuth in Microservices?
OAuth 2 is an authorization framework, a security concept for rest API( Read as MicroService), about how you authorize a user to get access to a resource from your resource server by using token. OAuth 2 has 4 different roles in this process.
How use OAuth 2.0 for REST API calls in C#?
- Step 1: Implement OAuth 2.0 Resource Owner Password Credential Flow. …
- Step 2: Add method “GenerateUserIdentityAsync” to “ApplicationUser” class. …
- Step 3: Issue JSON Web Tokens instead of Default Access Tokens.
How can I get OAuth2 token?
To do so, send a POST request to the OAuth2 Token URL: . The post request should be sent with a content type of x-www-form-urlencoded and include the following parameters: grant_type: The method you are using to get a token.
How do I get an OAuth 2.0 authentication token in C#?
Auth URL (which happens to be a “) if that helps. Access Token URL “” ClientId “abc”
What is nonce and state?
As you noted, state is for CSRF prevention while nonce is to prevent replay attacks in the single-page login flow since unlike the other flows it can’t pass along the client secret.
Does OAuth prevent CSRF?
1 Answer. If a resource is protected by OAuth 2 alone and an attacker gets client_id, client_secret and an access token, then no CSRF is needed at all.
What is OAuth PKCE?
PKCE is an OAuth 2.0 security extension for public clients on mobile devices intended to avoid a malicious programme creeping into the same computer from intercepting the authorisation code. … It allows applications to use the most reliable OAuth 2.0 flows in public or untrusted clients – the Authorization Code flow.
What is https reverse proxy?
A reverse proxy is a server that sits in front of web servers and forwards client (e.g. web browser) requests to those web servers. Reverse proxies are typically implemented to help increase security, performance, and reliability.