What is the best example of personally identifiable information
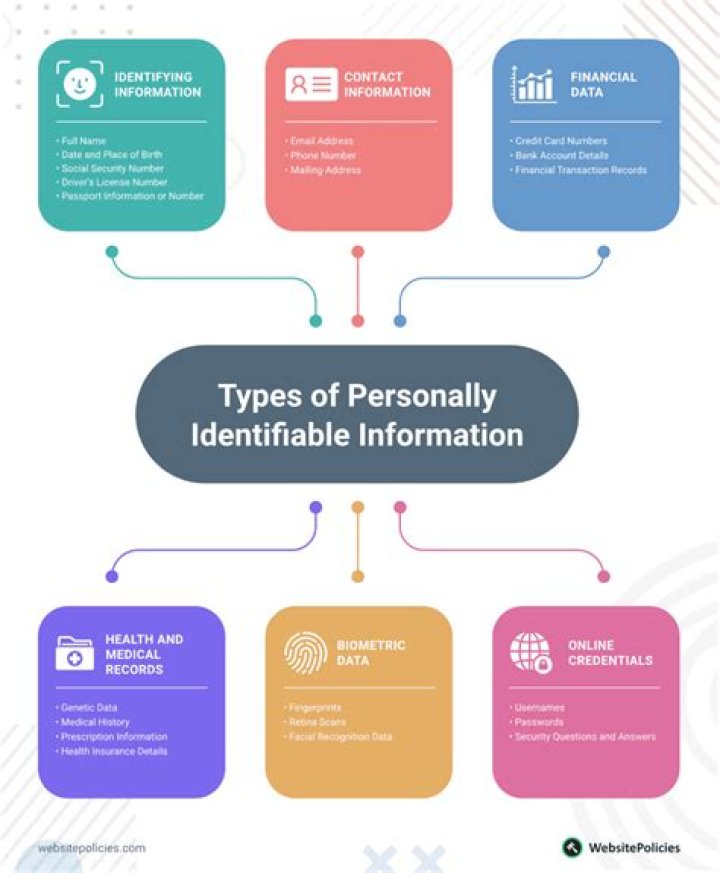
Examples of personally identifiable information (PII) include : Social security number (SSN), passport number, driver’s license number, taxpayer identification number, patient identification number, and financial account or credit card number. Personal address and phone number.
What are three examples of personally identifiable information quizlet?
Personally Identifiable information (PII) is any information about an individual maintained by an organization, including information that can be used to distinguish or trace an individual’s identity like name, social security number, date and place of birth, mother’s maiden name, or biometric records.
What are three examples of personally identifiable information choose three?
Personal identification numbers: social security number (SSN), passport number, driver’s license number, taxpayer identification number, patient identification number, financial account number, or credit card number. Personal address information: street address, or email address.
What is an individual's personally identifiable information considered cyber awareness?
information that can be used to locate or identify an individual, such as names, aliases, Social Security numbers, biometric records, and other personal information that is linked or linkable to an individual.Which of the following are examples of personally identifiable information PII quizlet?
PII means information that can be linked to a specific individual and may include the following: Social Security Number; DoD identification number; home address; home telephone; date of birth (year included); personal medical information; or personal/private information (e.g., an individual’s financial data).
Which definition best describes personally identifiable information?
Personally identifiable information (PII) refers to information employed by a company or organization to identify someone, make contact with them, or find them.
What are two example of personally identifiable information?
Sensitive personally identifiable information can include your full name, Social Security Number, driver’s license, financial information, and medical records. Non-sensitive personally identifiable information is easily accessible from public sources and can include your zip code, race, gender, and date of birth.
What three items are components of the CIA triad?
The CIA triad refers to an information security model made up of the three main components: confidentiality, integrity and availability. Each component represents a fundamental objective of information security.What are two examples of personally identifiable information PII Choose 2?
- Full name.
- Home address.
- Email address.
- Social security number.
- Passport number.
- Driver’s license number.
- Credit card numbers.
- Date of birth.
Malicious code is the term used to describe any code in any part of a software system or script that is intended to cause undesired effects, security breaches or damage to a system. Malicious code is an application security threat that cannot be efficiently controlled by conventional antivirus software alone.
Article first time published onWhich two characteristics are examples of poor passwords?
- Repeating previously used passwords.
- Names of close family members or friends.
- Your name.
- Words in the dictionary.
- Common names.
- Repeating your login code.
- Keyboard patterns and swipes (i.e., 123456 or QWERTY)
Which of the following is not considered personally identifiable information quizlet?
Terms in this set (20) Which of the following items would generally NOT be considered personally identifiable information (PII)? Explanation: A trade secret is not PII. PII is information that you can use to uniquely identify an individual.
What does PII stand for quizlet?
PII stands for. Personally Identifiable Information. What is PII ? information that can be used on its own, or with other information, to identify, contact, or locate a single person, or to identify an individual in context. PHI stands for.
What is an individual's PII or PHI considered quizlet?
What is an individual’s Personally Identifiable Information (PII) or Protected Health Information (PHI) considered? Sensitive information.
Which of the following is not an example of PII?
Info such as business phone numbers and race, religion, gender, workplace, and job titles are typically not considered PII. But they should still be treated as sensitive, linkable info because they could identify an individual when combined with other data.
What is considered PII under GDPR?
GDPR PII Definition PII or Personal Identifiable Information is any data that can be used to clearly identify an individual.
What are the primary motivations of the hacktivist?
- The appreciation of their country’s leaders.
- Food, wine, and gambling.
- Political, social, or moral disagreements.
- The cost of commercial software and support.
What central component is necessary for a botnet?
To build a botnet, botmasters need as many infected online devices or “bots” under their command as possible. The more bots connected, the bigger the botnet. The bigger the botnet, the bigger the impact.
What description best explains cybersecurity?
Cyber security refers to the body of technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access. Cyber security may also be referred to as information technology security.
What is not personal information?
Related Definitions Non-Personal Information means information or content other than Personal Information, including, for example, aggregated or anonymized information about our users and other information that does not identify any individual. Sample 1. Sample 2.
What are the PII personally identifiable information confidentiality impact levels?
Definition(s): The PII confidentiality impact level—low, moderate, or high— indicates the potential harm that could result to the subject individuals and/or the organization if PII were inappropriately accessed, used, or disclosed.
What is CIA triad explain with example?
A key concept to understand about the CIA triad is that prioritizing one or more principles can mean the tradeoff of others. For example, a system that requires high confidentiality and integrity might sacrifice lightning-speed performance that other systems (such as ecommerce) might value more highly.
What are the three main types of networks that must be considered when defining a security policy?
There are three components of network security: hardware, software, and cloud services.
What is an example of hacktivism CCNA?
What is an example of “hacktivism”? A group of environmentalists launch a denial of service attack against an oil company that is responsible for a large oil spill. You just studied 12 terms!
Which definition best describes social engineering?
Social engineering is the term used for a broad range of malicious activities accomplished through human interactions. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.
What is an example of malicious code?
Taking advantage of common system vulnerabilities, malicious code examples include computer viruses, worms, Trojan horses, logic bombs, spyware, adware, and backdoor programs. Visiting infected websites or clicking on a bad email link or attachment are ways for malicious code to sneak its way into a system.
What are some examples of malicious code cyber awareness?
3) Malicious Code Malicious code includes viruses, trojan horses, worms, macros, and scripts. They can damage or compromise digital files, erase your hard drive and/or allow hackers access to your PC or mobile from a remote location.
What type of attacker is most likely to use information you have posted about yourself?
Social engineers scour the Internet searching for any kind of information they can find on a person. The more information you have posted about yourself, the more likely it is that a criminal can send you a targeted spear phishing attack. Install and update antivirus and other software.
What are the 3 best practices to secure your password?
- Never reveal your passwords to others. …
- Use different passwords for different accounts. …
- Use multi-factor authentication (MFA). …
- Length trumps complexity. …
- Make passwords that are hard to guess but easy to remember.
- Complexity still counts. …
- Use a password manager.
What is an example of a weak password?
EXAMPLES OF WEAK PASSWORDS Any word that can be found in a dictionary, in any language (e.g., airplane or aeroplano). A dictionary word with some letters simply replaced by numbers (e.g., a1rplan3 or aer0plan0). A repeated character or a series of characters (e.g., AAAAA or 12345).
What does personally identifiable information include?
Further, PII is defined as information: (i) that directly identifies an individual (e.g., name, address, social security number or other identifying number or code, telephone number, email address, etc.) or (ii) by which an agency intends to identify specific individuals in conjunction with other data elements, i.e., …