Are hash functions random
A hash function is a “random oracle” You give it an arbitrarily-sized input. … If so, it gives you those 256 random bits as output. If not, it flips 256 random coins, associates them to this input, and gives you the coins as output.
Is sha256 truly random?
The SHA-256 (as well as any cryptographically secure hash algorithm) produces output that will appear like an uniformly random sequence to observer who does not know the input.
Are all hash functions the same?
Hash functions differ by type; however, there are several characteristics that persist between them. Deterministic: The hash value remains the same. No matter how many times you input a message into the hashing function you need to receive the same output.
Why is hash random?
The Solution. For the attacker to cause collisions in our hash map, he needs to know ahead of time what will cause them. … When the hash map is created we generate the random seed. This means that each hash map instance will convert the same key to a different index.What is uniform and random hash function?
One property of ideal random hash functions that seems intuitively useful is uniformity. A. family H of hash functions is uniform if choosing a hash function uniformly at random from H. makes every hash value equally likely for every item in the universe: Uniform: Pr.
Why is rehashing needed?
Why rehashing? Rehashing is done because whenever key value pairs are inserted into the map, the load factor increases, which implies that the time complexity also increases as explained above. This might not give the required time complexity of O(1).
How do hashes work?
A hash function is a mathematical function that converts an input value into a compressed numerical value – a hash or hash value. Basically, it’s a processing unit that takes in data of arbitrary length and gives you the output of a fixed length – the hash value.
What is global depth and local depth in extendible hashing?
They denote the number of bits which are used by the hash function to categorize the keys. Global Depth = Number of bits in directory id. Local Depth: It is the same as that of Global Depth except for the fact that Local Depth is associated with the buckets and not the directories.What is random probing?
In random probing a pseudo-random number generator is used to obtain a random sequence R(i), 1 <= i < b where R(1) , R(2), … R(b-1) is a permutation of [1, 2, …, b-1] . The buckets are examined in the order f(k) , (f(k)+R(i)) % b , 1 <= i < b . Quadratic Probing.
Can we reverse hash value?Hash functions are not reversible in general. MD5 is a 128-bit hash, and so it maps any string, no matter how long, into 128 bits. Obviously if you run all strings of length, say, 129 bits, some of them have to hash to the same value.
Article first time published onHow long is a SHA 256 hash?
A sha256 is 256 bits long — as its name indicates.
Why are hash functions irreversible?
2 Answers. It is irreversible in the sense that for each input you have exactly one output, but not the other way around. There are multiple inputs that yields the same output. For any given input, there’s a lot (infinite in fact) different inputs that would yield the same hash.
Is there a perfect hash function?
In computer science, a perfect hash function h for a set S is a hash function that maps distinct elements in S to a set of m integers, with no collisions. … A perfect hash function can, as any hash function, be used to implement hash tables, with the advantage that no collision resolution has to be implemented.
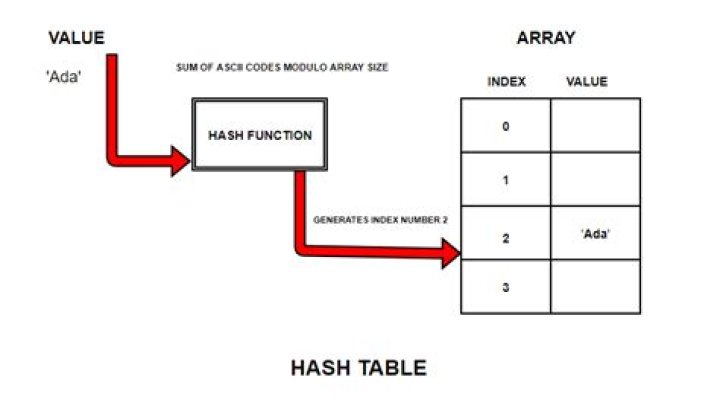
What is a hash function in data structure?
Definition: A hash function is a function that takes a set of inputs of any arbitrary size and fits them into a table or other data structure that contains fixed-size elements. … The table or data structure generated is usually called a hash table.
Which of the following is not a use of a hash function?
Which one of the following is not an application hash functions? Explanation: Key wrapping is a separate algorithm and not an application of hash fuctions.
Is hash irreversible?
While the hash produced is irreversible, it’s not pre-image resistant! Given the hash value of 0, I can very easily produce any number of inputs that produce that hash: 2, 4, 6, 8, 10, etc.
What is the purpose of hash function?
Hash functions are used for data integrity and often in combination with digital signatures. With a good hash function, even a 1-bit change in a message will produce a different hash (on average, half of the bits change). With digital signatures, a message is hashed and then the hash itself is signed.
Why does hashing not guarantee the authenticity of the data?
That said, some hashing algorithms cannot guarantee data integrity as well as others, either by virtue of not having been built for security purposes or due to advancements in computation that render older algorithms obsolete.
Is rehashing a collision resolution?
Rehashing is a collision resolution technique. Rehashing is a technique in which the table is resized, i.e., the size of table is doubled by creating a new table. … In such situations, we have to transfer entries from old table to the new table by re computing their positions using hash functions.
What is not possible with hash table?
There are some operations which are not efficiently supported by hash tables, such as iterating over all the elements whose keys are within a certain range, finding the element with the largest key or smallest key, and so on. The O(n) complexity is on average.
What is rehashing explain with example?
(Entry 1 of 2) transitive verb. 1 : to talk over or discuss again. 2 : to present or use again in another form without substantial change or improvement.
What is linear probing in hash table?
Linear probing is a scheme in computer programming for resolving collisions in hash tables, data structures for maintaining a collection of key–value pairs and looking up the value associated with a given key. … Along with quadratic probing and double hashing, linear probing is a form of open addressing.
What is step size in hashing?
stepSize = constant – ( key % constant ) The constant is a prime number and smaller than the array size. Double hashing requires that the size of the hash table is a prime number.
What is double hashing in data structure?
Double hashing is a computer programming technique used in conjunction with open addressing in hash tables to resolve hash collisions, by using a secondary hash of the key as an offset when a collision occurs. Double hashing with open addressing is a classical data structure on a table .
How extendible hashing is different from linear hashing?
Extendible hashing uses 9 pages including the directory page(assuming it spans just one page) and linear hashing uses 10 pages. and the usual hash functions for both and a page capacity of 4 records per page. Extendible hashing takes 4 data pages and also a directory page whereas linear hashing takes just 4 pages.
What is are true about extendible hashing?
Extendible hashing is a new access technique, in which the user is guaranteed no more than two page faults to locate the data associated with a given unique identifier, or key. Unlike conventional hashing, extendible hashing has a dynamic structure that grows and shrinks gracefully as the database grows and shrinks.
What is the difference between linear hashing and extendible hashing?
Extendible Hashing: no overflow pages and gets data always on 1st/2nd hit. Linear Hashing: can handle duplicate keys and does not need directory.
Can we decrypt hash?
As commenters have mentioned, you cannot decrypt a hash. Hashing and encryption/decryption are two separate operations. Encryption and decryption are opposites, while hashing has no opposite function. … As you can see from the table, there’s no way to get back to the original letter knowing only the hash value.
Is hash a cryptography?
Hashing is a method of cryptography that converts any form of data into a unique string of text. Any piece of data can be hashed, no matter its size or type. In traditional hashing, regardless of the data’s size, type, or length, the hash that any data produces is always the same length.
How many possible md5 hashes are there?
While it is likely that you get collisions if the values to be hashed are much longer than the resulting hash, the number of collisions is still sufficiently low for most purposes (there are 2128 possible hashes total so the chance of two random strings producing the same hash is theoretically close to 1 in 1038).
Why is SHA256 irreversible?
SHA256 is a hashing function, not an encryption function. Secondly, since SHA256 is not an encryption function, it cannot be decrypted. What you mean is probably reversing it. In that case, SHA256 cannot be reversed because it’s a one-way function.



